Deepfake Investment Scams: What You Need to Know
🛡️ Adviser Briefing: Deepfake Investment Scams Targeting the Public
Why This Matters
As a trusted financial advisory firm, we are seeing a rise in AI-generated deepfake scams that are misleading the public with fake endorsements from high-profile figures. These scams are not only damaging to individuals but also undermine trust in legitimate financial advice.

 This briefing is designed to help you:
This briefing is designed to help you:
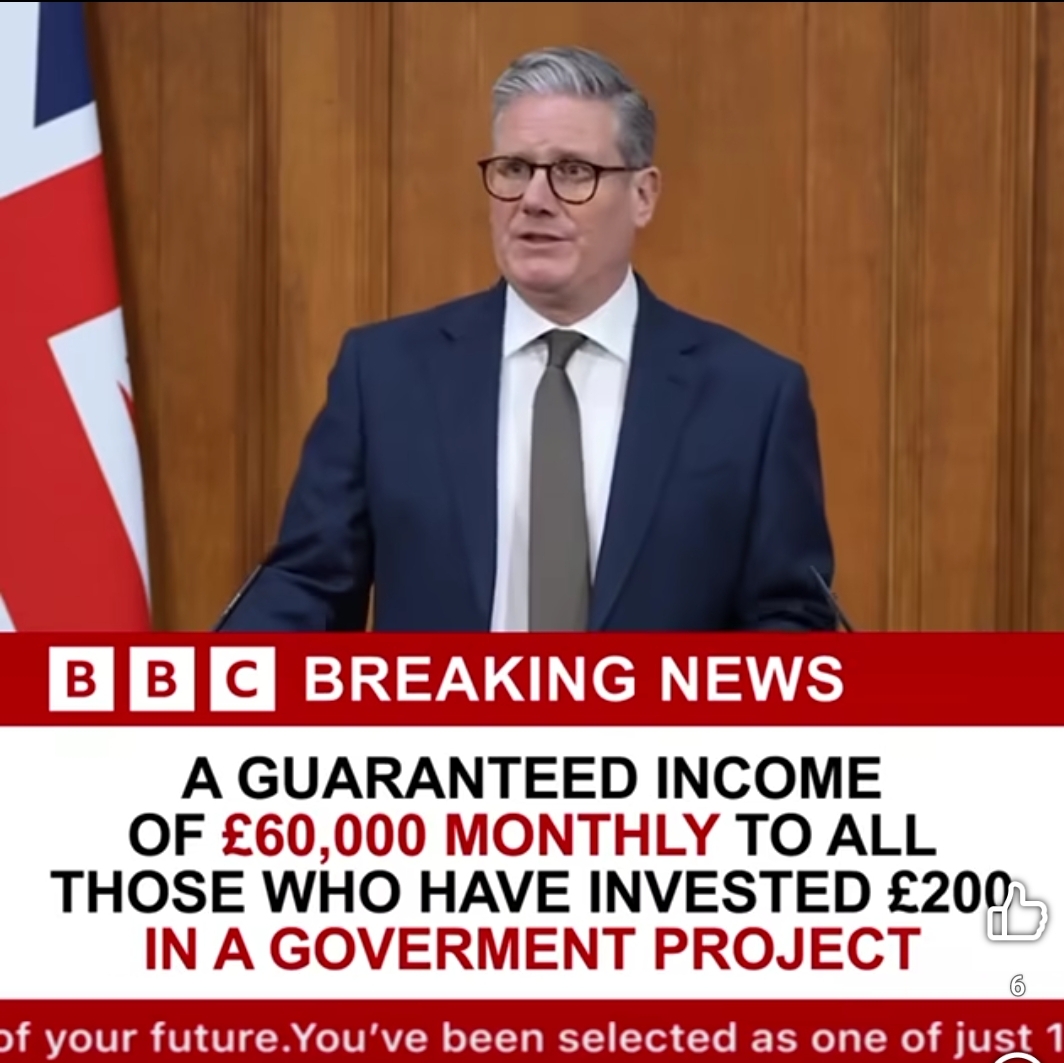
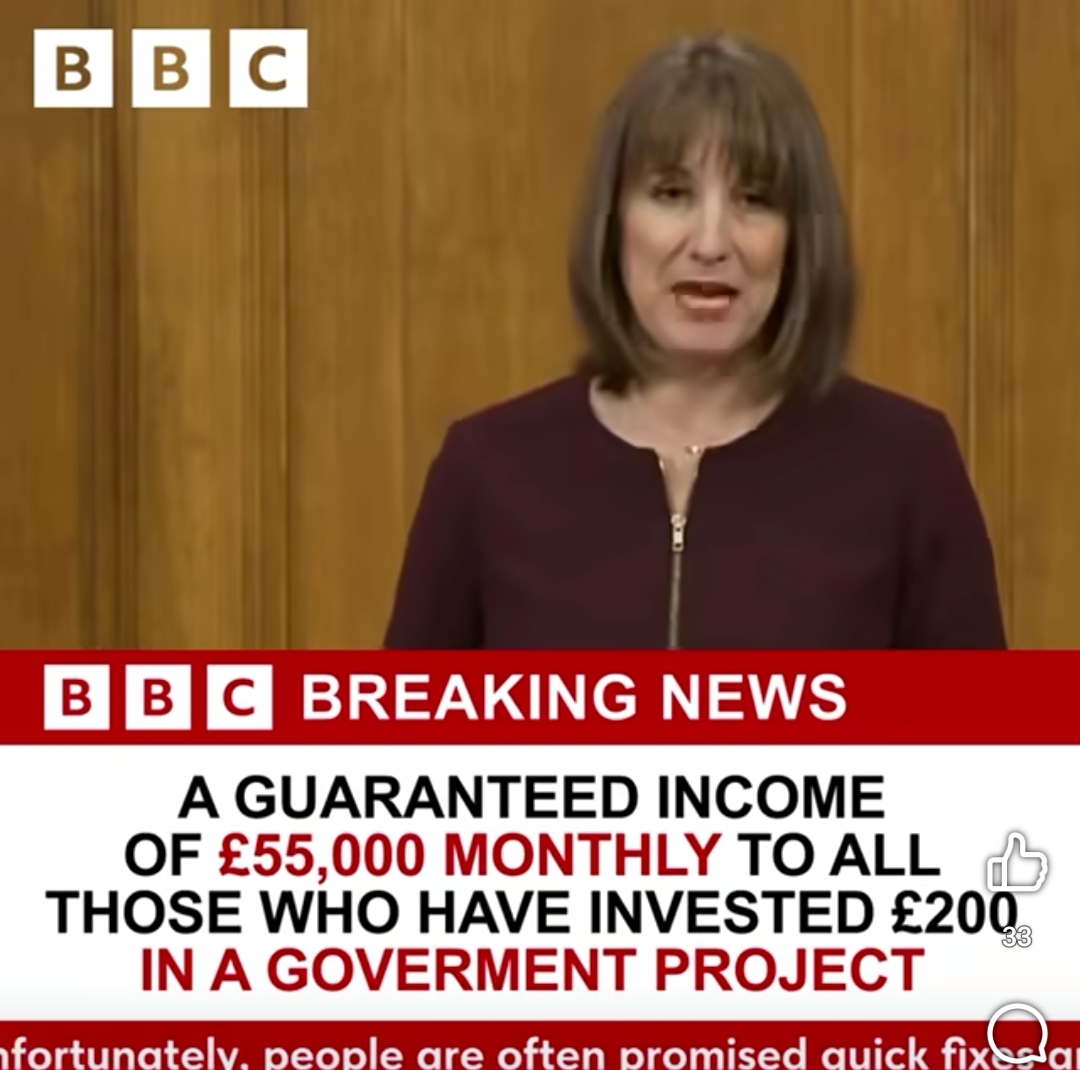
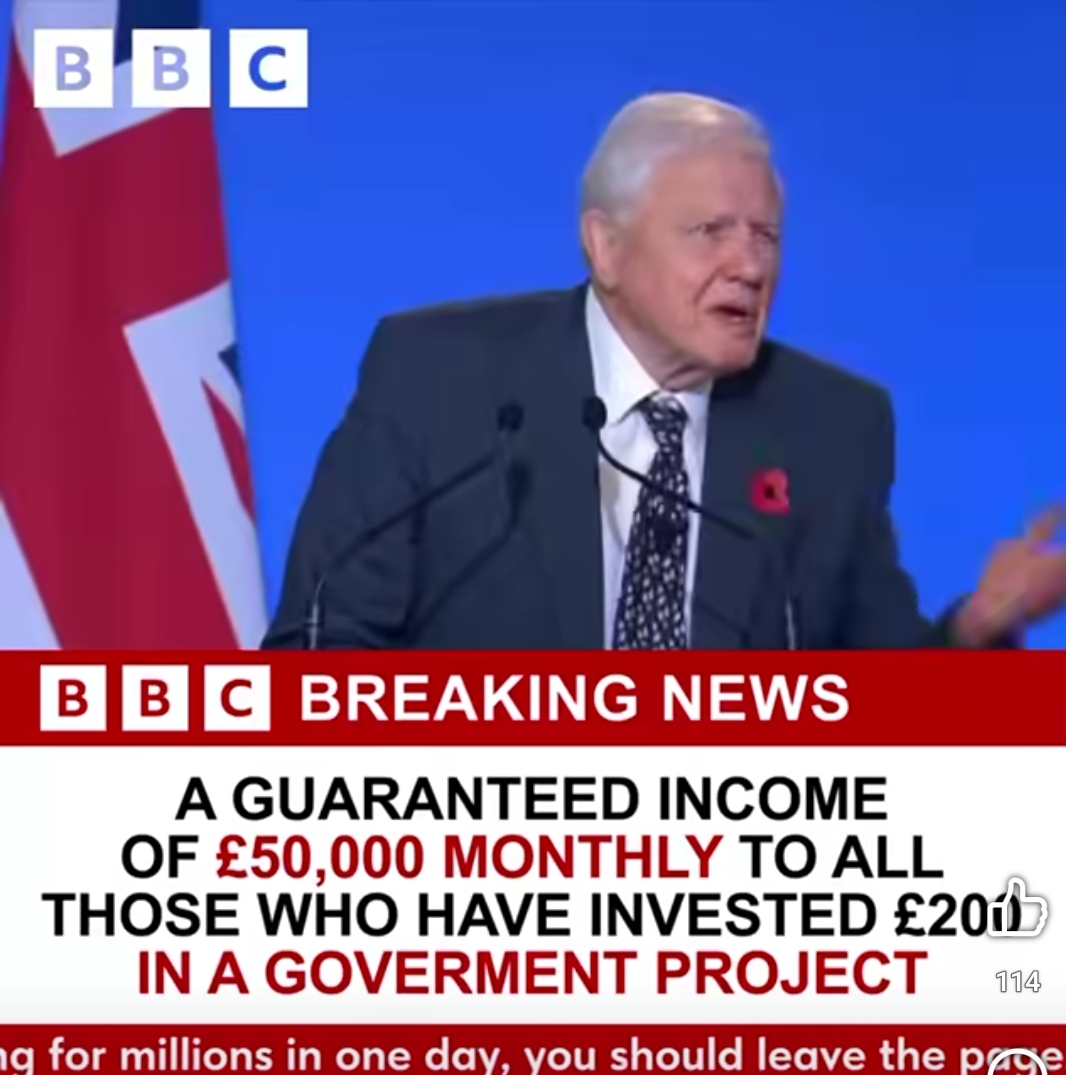
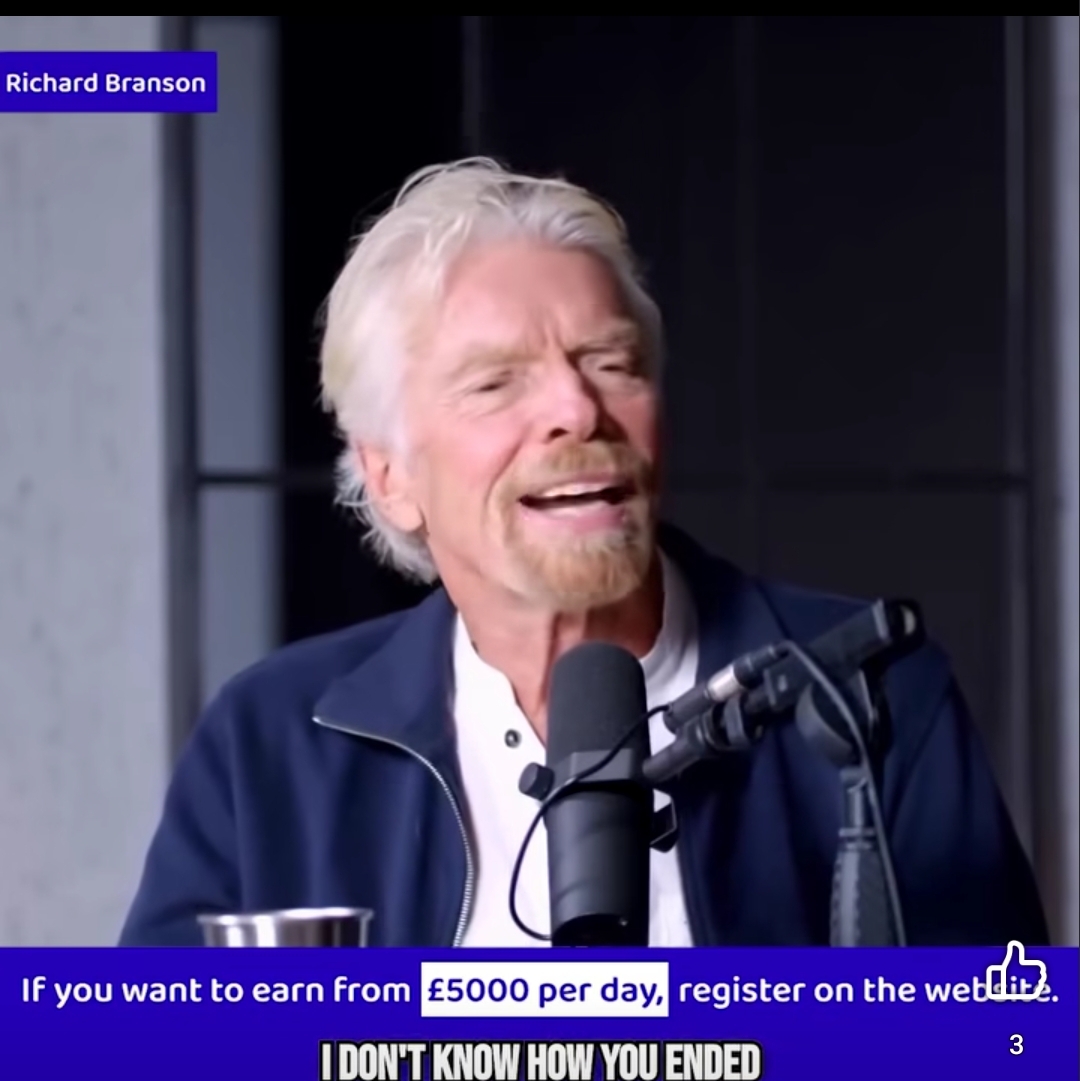
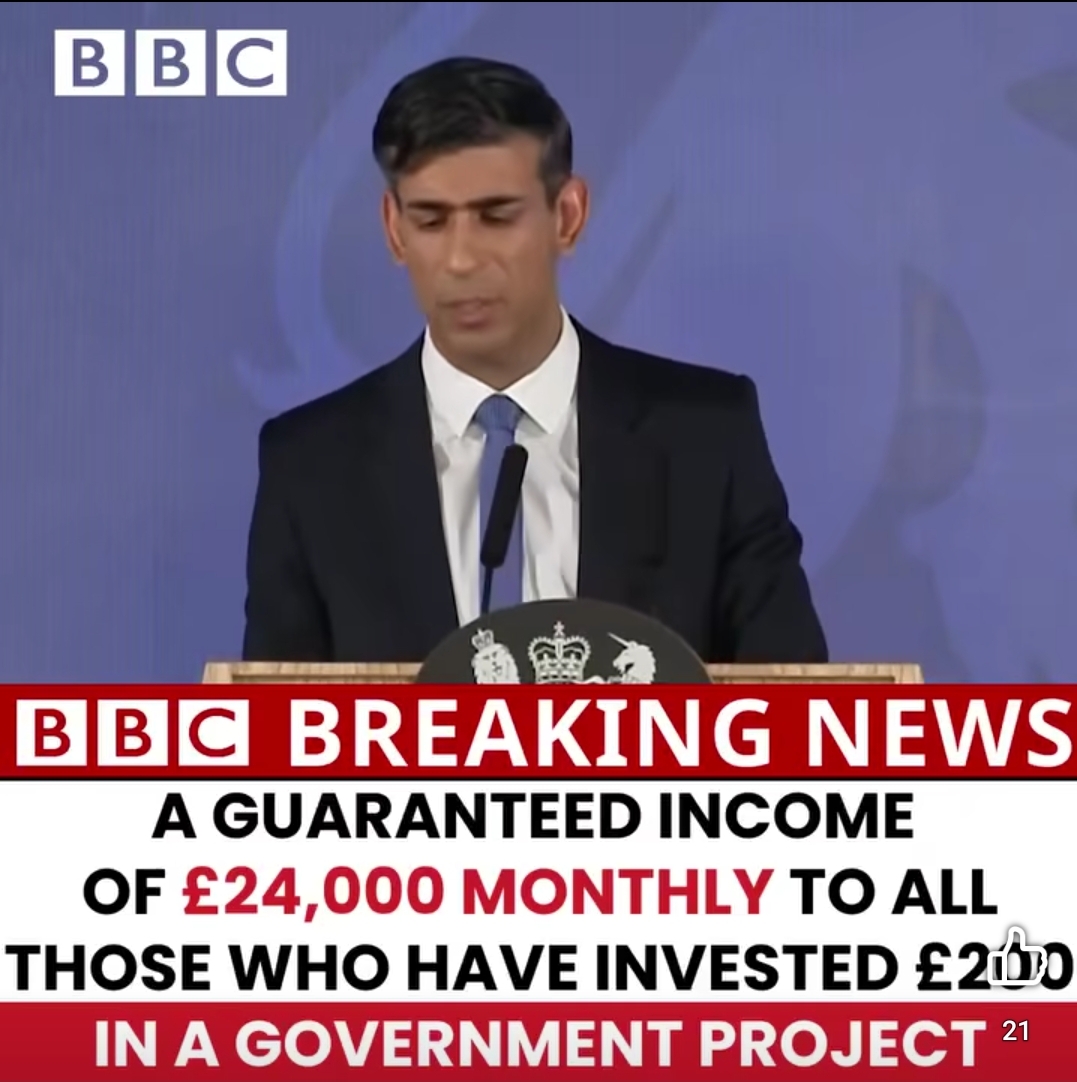
- Recognize the signs of deepfake scams. Quite often these videos are taken from existing footage of these people already online, from conferences or locations where they may have been in the past but may not appear currently. For example Downing Street, a party conference, or a climate conference. They may also be slightly grainier or stuttered to try and disguise the overlaying of motion in the fake. The endorsements may also try and pass off from legitimate news sources, or establishments, such the BBC, Sky News, The Bank of England, or the FCA, as you can see from the capture images below. These are all actual captures of the videos that I have seen myself in the last few days. All offering similar products, and from a couple of different social media platforms.
- Educate clients who may have seen or fallen for these scams.
- Report any suspicious activity or client disclosures.
🎭 What Are Deepfake Investment Scams?
Scammers are using AI to create realistic videos and audio clips of public figures—such as Rishi Sunak, Martin Lewis, Richard Branson, Keir Starmer, and even Sir David Attenborough—promoting fake investment opportunities. These videos are often:
- Shared on social media or messaging apps.
- Embedded in fake news articles or spoofed websites.
- Promoted via paid ads that appear legitimate.
The goal is to lure viewers into depositing money into fraudulent platforms, often under the guise of cryptocurrency or “government-backed” schemes.
🧠 Why Clients Are Falling for It
These scams are convincing because:
- The videos look and sound authentic.
- They use trusted public figures to build credibility. Particularly in high business, political influence or people in the financial world whom the opinions of, are trusted.
- They promise quick, guaranteed returns.
- They create a sense of urgency (“limited-time offer”).
Some clients may even receive fake “returns” initially, which encourages them to invest more before the scammers vanish.
🚩 Red Flags to Discuss with Clients
Encourage clients to be cautious if they encounter:
- Celebrity endorsements of financial products online.
- Unsolicited investment opportunities via email, social media, or messaging apps.
- High-pressure tactics urging immediate investment, or low value high return incentives.
- Unfamiliar platforms or websites that mimic legitimate institutions.
🗣️ Talking Points for Client Conversations
- “Have you seen any investment videos online recently that seemed too good to be true?”
- “If you ever see a public figure promoting an investment, feel free to run it by us first.”
- “We’re seeing a rise in AI-generated scams—if anything feels off, it probably is.”
✅ What You Should Do
- Stay alert: If a client mentions a suspicious video or offer, take note.
- Report it: Share any examples or client disclosures with our compliance team.
- Educate: Use this as an opportunity to reinforce the value of regulated, professional advice.
I hope this will help you and your clients spot these Deep Fake scams, and more so no one has yet fallen for them without due care and consideration. This hasn’t been the first set in this type of scam, and its very unlikely to be to be the last, as AI and of course deep fakes, become better and cleverer in the coming months and years.
Thanks for reading
Dan
